Why It’s Essential for Modern Cybersecurity In today’s digitally-driven world, the traditional perimeter-based security model is no longer sufficient. With the rise of remote work, cloud services, and sophisticated cyber…
Month: July 2024

The Five Biggest Cloud Security Threats
(And how to deal with them) Cloud computing has transformed business operations by enabling remote storage of data and applications, boosting agility and efficiency. However, this shift also brings potential…
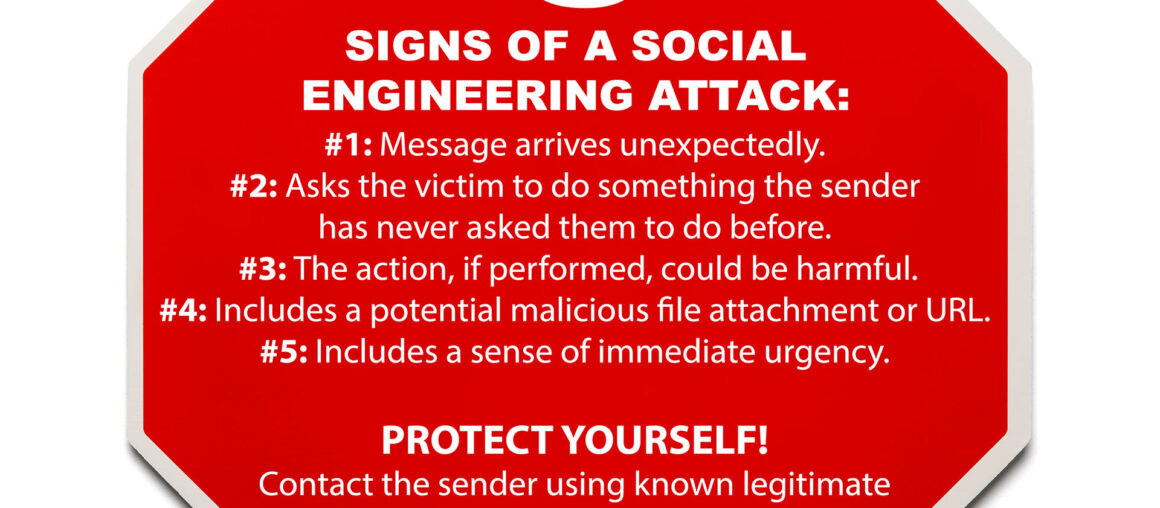
5 Signs of Social Engineering
Legitimate emails can exhibit these traits, but messages with three or more of them are at a higher risk of being part of a social engineering attack. Most social engineering…

TOAD Attack
What is a TOAD Attack? A TOAD attack, which stands for Telephone-Oriented Attack Delivery, is a relatively new type of phishing attack that combines voice and email phishing techniques. In…

Understanding Vendor Imposter Schemes: The Growing Threat to Businesses
What is a Vendor Imposter Scheme?A vendor imposter scheme is a type of fraud where cybercriminals impersonate legitimate vendors to deceive businesses into transferring funds into fraudulent accounts. These schemes…




